The Shifting Landscape of Healthcare Cyberattacks in 2025
In recent months, healthcare organizations have been facing a dramatic surge in ransomware incidents. Recent research by experts at Comparitech, for example, shows that in the first nine months of 2025, hospitals, clinics, and other direct care providers experienced 293 attacks – a worrying sign that cybercriminals have refined their plans. While attacks on healthcare providers seem to have slightly declined compared to previous periods, the rate of strikes against healthcare businesses, including vendors and service partners, has risen by roughly 30%. This editorial takes a closer look at the tricky parts of this shifting cyber threat environment and what it means for the industry.
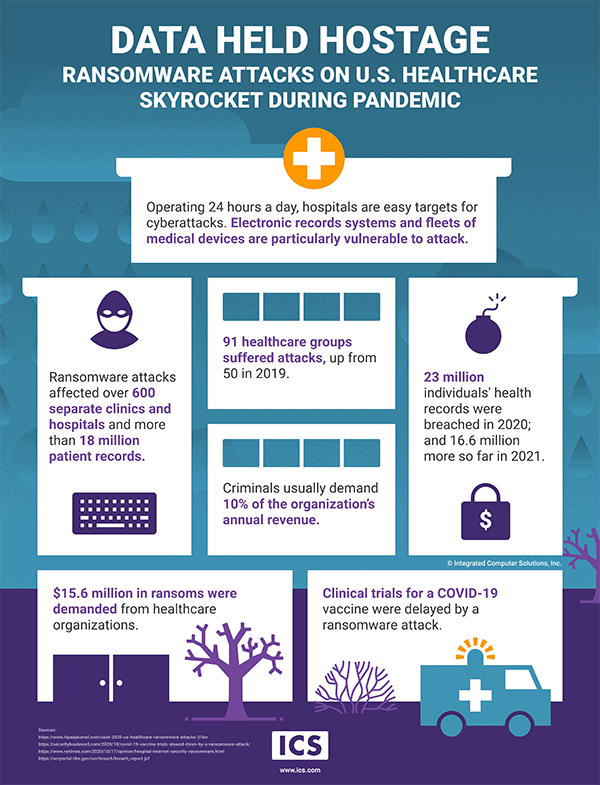
Cybersecurity in healthcare has always been a sensitive topic. From breaches that expose millions of patient records to nerve-racking ransom demands, every incident reminds us that the industry cannot afford to ignore the security gaps in its IT and OT systems. With vendors and service partners now in the crosshairs, the network of connections that healthcare organizations rely on is becoming loaded with issues that demand immediate attention.
Understanding the Rising Tide of Ransomware Attacks
As reported by various accounts, the healthcare sector in 2025 has seen ransomware attacks that are both intimidating and multifaceted. Cybercriminal groups – with names like INC, Qilin, SafePay, RansomHub, and Medusa – are consistently engaging with healthcare institutions worldwide. The ransom demands themselves, averaging about US$514,000 to US$532,000 for confirmed incidents, paint a picture of a sector that is vulnerable and loaded with problems.
Many experts note that the twist and turns of these ransomware campaigns have evolved. Whereas earlier cyberattacks focused solely on medical providers, more recent strikes target businesses that handle healthcare data – such as billing companies, pharmaceutical manufacturers, and technology vendors. This means that even if a hospital has fortified its internal systems, third-party providers sometimes remain as the weak link in the network.
Key Figures and What They Mean
Some of the numbers from 2025 are eye-opening. For instance:
- 293 ransomware incidents recorded on direct care providers.
- An additional 130 attacks targeting businesses in the healthcare sector.
- The total ransomware-related breaches in the United States trailed at 257, with other major markets like Australia, Germany, and the United Kingdom also showing worrying rates.
What is perhaps most concerning is not just the frequency but the quantity of records compromised. In one notable case, the ransomware group Qilin claimed to have stolen over 11.1 terabytes of data from a top-tier healthcare institution. Numbers like these underline the nerve-racking scope of the problem.
Third-Party Vulnerabilities: A New Target for Cybercriminals
One of the most complicated pieces of the current cyber threat puzzle is the shift in attack vectors. Previously, cybercriminals primarily focused on hospitals themselves. However, the landscape has evolved. Today, even if healthcare providers have updated systems and employee training programs, vendors – from payment service providers to IT consultants – are increasingly becoming their primary target.
This trend means that healthcare organizations must now figure a path through not only their own internal security measures but also the security of partners in their extended network. In many cases, a single vendor’s lack of updated security can expose multiple healthcare organizations to tremendous risk.
Challenges in Managing Vendor Cybersecurity
When thinking about third-party cybersecurity risks, several tangled issues come to mind:
- Trust versus Verification: Organizations often place high trust in their vendors; however, relying solely on trust without proper verification can open the door to hidden vulnerabilities.
- Diverse Security Standards: Vendors come from various segments of the market with different security protocols, which can make it intimidating to establish a uniform defense mechanism.
- Collaboration and Data Sharing: Shared infrastructure means that a breach at one point in the network can have rippling effects across many organizations.
To manage these risks, healthcare institutions and their partners must take a closer look at how they collaborate. They need to work through the fine points of cybersecurity contracts, insisting on regular audits and adherence to essential security standards that minimize the small distinctions that can be exploited by attackers.
Ransomware Strains: The Acting Villains
Cybercriminal groups continue to use a range of ransomware strains to execute their plans. Even though each strain has its own particular characteristics, there are several that stand out for their activity and danger. For instance, INC has become notorious for its intensive campaigns against healthcare providers, while Qilin has made headlines by targeting businesses and even by stealing a massive 11.1 terabytes of data from one institution.
Analysts have taken a closer look at the nitty-gritty details of these strains. Let’s dive in by considering some of the key players:
| Ransomware Strain | Sector Targeted | Notable Record Breaches | Ransom Demand (Average) |
|---|---|---|---|
| INC | Healthcare Providers | Over 20.1 TB claimed | ~US$514,000 |
| Qilin | Healthcare Businesses | More than 11.1 TB stolen | ~US$532,000 |
| SafePay | Mixed | Significant data leaks reported | Varies |
| RansomHub | Both sectors | Multiple breaches | Varies |
| Medusa | Healthcare Providers | Several incidents confirmed | Varies |
This table highlights some of the major players and points out that each ransomware strain can have a tailored impact on either the healthcare provider or the supporting business. The double threat means that even organizations with robust defensive measures must remain vigilant.
Why Healthcare Is a Prime Target
There are several reasons why the healthcare sector is so alluring to cybercriminals. First, the data involved is deeply personal and sensitive – making it extremely valuable on the black market. Second, digitization in healthcare has led to the adoption of old protocols and legacy systems, which may be more open to exploitation. Finally, as healthcare operations increasingly rely on interlinked vendor networks, there are many points of potential entry.
Providers are also subject to legal and regulatory pressures that make them more likely to pay a ransom under duress than companies in some other sectors. When lives and patient care are at stake, the idea of taking a calculated risk by paying a ransom can seem like the lesser of two evils. Yet, the consequences of paying also set a dangerous precedent that may encourage further attacks in the future.
The Hidden Complexities of Patient Data Security
Healthcare organizations deal with patient data that is more than just a record—it represents the trust between a patient and the caregiver. This trust can be jeopardized by even a single breach, leading to reputational harm aside from legal and financial consequences. In addition to internal security measures, these institutions need to account for the subtle parts of vendor relationships where data might flow, storing and processing in ways that are not always transparent.
The nitty-gritty details involve not only encrypting data and ensuring secure endpoints but also verifying that partner vendors comply with the same super important data protection standards. This alignment is critical to avoid having the whole chain pulled into a security breach.
Practical Steps to Bolster Cyberdefense in Healthcare
Given the rising threat, healthcare institutions and their network partners need to work through the tangled issues and figure a path toward a more secure future. Here are some steps that can help:
Enhance Employee and Vendor Training
Because many attacks start with phishing or social engineering, it is essential for employees to be well trained in security best practices. Providers should not only educate their own workforce, but they must also collaborate closely with vendors to ensure that everyone in the network can steer through the confusing bits of evolving cyber threats.
Best practices include:
- Regular security awareness sessions using real-world examples to illustrate how attackers operate.
- Simulated phishing exercises that help staff identify and report suspicious emails.
- Vetting suppliers with mandatory cybersecurity training and periodic audits.
Invest in Advanced Threat Detection
With the cyber threat environment evolving, organizations need to dig into sophisticated threat detection tools. Intrusion detection systems that are tailored for industrial control systems and healthcare IT environments can rapidly alert teams to unusual activity. This is especially critical in times when every minute counts in mitigating an ongoing attack.
Modern detection systems can “poke around” in network traffic, identifying the subtle details of suspicious behavior while balancing the need for uninterrupted patient care. Investing in these technologies might seem overwhelming at first, but they represent a must-have component of any comprehensive cybersecurity strategy.
Implement Regular Cybersecurity Audits
One of the most effective ways to get into the nitty-gritty of your security posture is to conduct regular audits. External audits and penetration testing can unearth hidden vulnerabilities that internal teams might overlook. These assessments ensure that the infrastructure is not only updated but also that any tangled issues in the network are addressed before cybercriminals can exploit them.
Audits should cover aspects such as:
- Verification of vendor security measures.
- Assessment of network segmentation and data flow controls.
- Testing backup and disaster recovery procedures.
- Review of compliance with industry standards and regulations.
Managing Your Way Through Complex Cyber Insurance Requirements
As ransomware attacks increase in frequency and intensity, cyber insurance is becoming a key part of risk management. However, many providers now face overwhelming terms and off-putting coverage gaps. With more insurers excluding coverage for nation-state or war-related incidents, filing claims can be as nerve-racking as the attacks themselves.
Healthcare organizations and their vendor partners should take practical steps when selecting cyber insurance:
- Review policy exclusions: Make sure that any policy you choose covers the full spectrum of risks. Policies that rely on the concept of “legitimate interest” should be examined closely to understand potential pitfalls.
- Negotiate terms where possible: Insurers may be willing to adjust terms when a business can demonstrate strong internal controls and proactive cybersecurity measures.
- Integrate insurance with security enhancements: Insurance should be seen as a backup—not a substitute—for investing in critical security upgrades.
Preparing for Future Cybersecurity Challenges in Healthcare
Looking ahead, the threat landscape is poised to become even more convoluted. Healthcare organizations are not only contending with targeted ransomware attacks; they must also keep abreast of evolving tactics and emerging vulnerabilities. Recent incidents have proven that even once reliable systems can be undermined by new, creative exploitation techniques.
For many, the challenge of staying one step ahead might feel practically insurmountable, but there are effective strategies to get around these issues:
Continuous Monitoring and Adaptive Strategies
One of the key lessons for 2025 is that cybersecurity is not a one-and-done effort. It requires a dynamic approach where monitoring is continuous and defensive measures are constantly adjusted to address new threats. When teams set up real-time monitoring and analysis systems, they can catch suspicious behavior early – sometimes even before an attack fully unfolds.
Adaptive defense strategies focus on:
- Real-time threat intelligence sharing between partners.
- Automated updates and patch management.
- Ongoing reviews of system architecture, with a focus on minimizing the tangled issues of outdated protocols.
Fostering a Culture of Cyber Resilience
Beyond technical measures, healthcare leaders must nurture a culture where security is every department’s responsibility. From the frontline nurse to the IT director, everyone should be aware of the delicate balance between operational continuity and security. This approach may appear overwhelming, but by breaking down tasks into manageable steps, organizations can gradually build a robust defense.
Some practical ways to foster cyber resilience include:
- Regular cross-departmental training sessions that explain the small distinctions between safe and unsafe digital practices.
- Simulation exercises that involve both internal staff and external partners.
- Clear communication channels during a crisis, so that everyone can find their way through the confusing bits of a security incident.
Long-Term Economic and Reputation Impacts
The consequences of a ransomware attack extend far beyond immediate financial costs. The loss of patient confidence, potential litigation, disruptions in care delivery, and long-term reputational damage can have a ripple effect on a healthcare organization’s viability. As cyberattacks shift their focus more frequently to vendors and third-party providers, the economic stakes become ever higher.
Industry leaders argue that while the upfront cost of cybersecurity investments might seem high, the price of inaction is far steeper. Small improvements in system updates, vendor oversight, and employee training can help mitigate expensive breaches.
Balancing Risk and Investment
Decision-makers must weigh the costs of implementing new security measures against potential losses from cyberattacks. Some of the key considerations include:
- The annual costs associated with healthcare data breaches.
- Potential regulatory fines and legal fees.
- Loss of patient trust and damage to a brand’s reputation.
- The opportunity costs of diverting resources from patient care to emergency damage control.
It is clear that investments in cybersecurity are not just an IT expense, but a critical aspect of overall business strategy. A proactive stance in these matters can help organizations avoid the overwhelming and intimidating outcomes of an actual breach.
Future Innovations and Cybersecurity Integration
As we move forward, emerging technologies promise to be both a boon and a challenge. For instance, the integration of edge AI and advanced analytics in cybersecurity may offer hope in identifying suspicious patterns amid a vast sea of data. Tools powered by artificial intelligence are starting to make sense of the little twists and subtle details that human analysts might miss.
However, these innovations come with their own set of tricky parts. The deployment and consistent management of advanced systems can be complicated. Organizations will need to dive in deeply, invest in high-quality training, and adapt quickly to the changing tech environment.
Key Areas of Technological Development
Some promising areas that may improve healthcare cybersecurity include:
- Edge AI for Threat Detection: Lightweight AI systems that can be placed at network edges to continuously monitor data flow and flag suspicious activity.
- Blockchain for Data Integrity: Distributed ledger technologies can help ensure that patient data remains untampered with, reducing the risk of fraudulent claims.
- Cloud Security Controls: As healthcare data increasingly migrates to cloud environments, advanced security protocols can help encrypt and protect sensitive information.
- Vendor Cybersecurity Rating Systems: Platforms that provide objective measures of vendor cybersecurity performance could ease the process of making sure that third-party partners are not the weak links.
By integrating these technologies, healthcare organizations may better address the confusing bits and hidden problems of their digital ecosystems.
Industry Collaboration and Regulatory Efforts
No single organization can solve the cybersecurity crisis alone. The current situation calls for a collaborative approach involving healthcare providers, vendors, insurers, governmental agencies, and industry coalitions. Legislative efforts – such as Senate bills aimed at reinforcing cybersecurity collaboration – are also gaining ground. These initiatives can help standardize what every organization should do to protect its data.
In parallel, companies are increasingly working through the regulatory maze to implement common frameworks that reduce the small distinctions in security measures. By fostering a more standardized ecosystem, the industry can hope to prune away the tangled issues that allow attackers to slip past individual defenses.
Steps Toward Greater Cooperation
To build a more resilient healthcare digital ecosystem, some of the recommended guidance includes:
- Establish cross-industry working groups to share threat intelligence.
- Develop joint incident response protocols that can be activated in unison.
- Advocate for government incentives to upgrade outdated systems and invest in next-generation cybersecurity technology.
- Create centralized vendor evaluation and cybersecurity scoring systems to help healthcare organizations easily see which partners pose higher risks.
These initiatives, while challenging to implement, are absolutely essential for creating a healthcare network that is more secure and better prepared for future attacks.
Lessons Learned from the 2025 Data
Every ransomware incident, every breach, and every ransom demand offers a lesson wrapped in the fine shades of cause and effect. In 2025, some major takeaways emerge:
- Who is being hit: While hospitals remain a prime target, the rising focus on healthcare businesses and third-party vendors means that the entire ecosystem must improve its defensive measures.
- What is at stake: Beyond financial losses, the exposure of personal data affects patient trust and can lead to significant long-term reputational damage.
- Which strains show up the most: Ransomware groups such as INC and Qilin dominate not only in terms of frequency but also when measured by the sheer volume of stolen data.
- How it happens: The tactics used by cyber criminals often involve exploiting the smallest differences in system defenses, making it paramount that organizations address even the minor details of security.
These lessons are central if healthcare organizations are to reduce their vulnerability by finding their way out of the maze of past mistakes.
A Call to Action for Healthcare Leaders
As we take a closer look at the numbers, the reality is both sobering and motivating. Cybersecurity in healthcare is not an abstract issue; it is a concrete challenge that directly affects patient care, trust, and operational sustainability. Leaders in this field must take a proactive stance that combines technology, training, and collaboration to stave off attacks that exploit every fine shade of vulnerability.
The current environment, with its nerve-racking ransom demands and overwhelming record breaches, forces decision-makers to prioritize cybersecurity investments. Whether it’s enhancing employee simulations, scheduling regular vendor audits, or embracing advanced threat detection tools, every step taken can make a significant difference.
Actionable Strategies for Moving Forward
In summary, those entrusted with protecting healthcare data should consider the following action plan:
- Audit and Update: Regularly assess both internal systems and vendor compliance to fix tangled issues before attackers can exploit them.
- Adopt Advanced Monitoring: Integrate AI-driven and edge-based detectors that are capable of flagging the small distinctions which reveal early signs of compromise.
- Enhance Collaboration: Work closely with third-party partners to establish common security standards and data sharing protocols that reduce the risk of an attack spreading across the network.
- Secure Cyber Insurance: Review and negotiate cyber policies carefully; insurance should be considered an essential backup plan rather than the primary line of defense.
- Government and Industry Engagement: Participate in industry-wide initiatives and policy-making processes that aim to improve cybersecurity baselines for the entire healthcare ecosystem.
Final Thoughts on Building a Resilient Future
The year 2025 has taught us that breaches and cyberattacks are not isolated incidents; they are reflections of a deeply interconnected challenge that spans organizational silos, technology stacks, and vendor relationships. Healthcare institutions must work on multiple fronts: adopting new technologies, enhancing human awareness, and building closer networks among partners.
While it might feel intimidating to grapple with these overwhelming threats, the alternative—waiting until the next big breach occurs—is even more off-putting. By addressing the subtle details of the cybersecurity maze and finding paths through its twists and turns, leaders can help safeguard patient trust and improve operational resilience.
As cybercriminals continue to sharpen their methods, it is essential that healthcare organizations keep their defenses equally agile. The journey ahead involves lots of tricky parts, tangled issues, and confusing bits that require careful, continuous attention—but the stakes are simply too high for anything less.
Ultimately, the call to action is clear: invest in robust cybersecurity, work hand in hand with vendors and partners, and maintain a persistent vigilance over all aspects of digital operations. For healthcare organizations, this proactive and comprehensive approach is not just a defensive measure—it is a cornerstone in preserving the trust, safety, and health of the communities they serve.
In a time when cyber threats are loaded with tension and every byte of stolen data could spell disaster for patient trust, the only responsible path is one of active engagement and continuous improvement. Healthcare security, in all its complicated pieces and nerve-racking demands, remains essential to saving lives—on and off the digital front.
Originally Post From https://industrialcyber.co/reports/healthcare-ransomware-attacks-surge-30-in-2025-as-cybercriminals-shift-focus-to-vendors-and-service-partners/
Read more about this topic at
Healthcare ransomware attacks surge 30% in 2025, as …
When ransomware kills: Attacks on healthcare facilities